You buy the hardware, but the system fails to track your inventory. This happens when you misunderstand the ecosystem. You need to master the balance between reading, writing, and software integration.
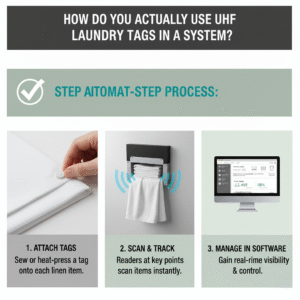
A UHF RFID reader system relies on radio waves to power passive tags and exchange data. While reading captures existing IDs, a robust RFID Write Reader encodes unique digital identities. Success depends less on the antenna range and more on the software compatibility that links these signals to your database.

Many people think hardware is the hard part. They are wrong. The real challenge lies in the invisible code that makes the hardware useful.
How Does the RFID Card Reader Work in a High-Speed Environment?
Fast-moving conveyor belts terrify inexperienced integrators. Missing a single tag disrupts the entire logistics chain. You need to understand the physics of the synchronization.
The reader emits a radio signal that wakes up the tag's chip. The tag responds with its data. In high-speed setups, this happens hundreds of times per second. A UHF Integrated Reader U6-IE-02 Long Range Reader manages this chaos by filtering signals and sending only verified data to your system.

A common question we receive is: "How does the RFID card reader work" in a high-speed environment? It is not magic; it is a synchronization of hardware and physics. The reader acts as the power source. Passive RFID tags do not have batteries. When the reader sends out a wave (UHF), the tag "harvests" that energy to wake up the chip and reflect its data back. This is called backscatter.
However, the distinction between a simple scanner and a robust RFID Write Reader is critical. Reading requires less power. Writing (or encoding) requires the reader to send a stronger, more focused burst of energy to physically alter the memory state of the chip. This is why writing usually requires the tag to be closer to the antenna than reading does.
To understand this fully, you must understand the memory banks of a tag. A tag is not just one long number. It is split into sections.
| Memory Bank | Function | Read/Write Ability |
|---|---|---|
| Reserved | Stores Access and Kill passwords | Secure Write |
| EPC | The main ID (Electronic Product Code) | Read & Write (Changeable) |
| TID | Unique Manufacturer ID | Read Only (Permanent) |
| User | Extra data (Exp. Date, Lot No.) | Read & Write |
In logistics, you mostly use the EPC bank. But in asset management, you might use the User bank to write maintenance records directly onto the equipment. If you use a UHF Long Range Reader U6-IE-02, you are mostly reading EPCs rapidly. If you are at a desk station, you are writing to the EPC and User banks. Knowing which operation you need determines the hardware you choose.
Why Is Reader Writer Software More Critical Than Hardware Specs?
A powerful engine is useless without a steering wheel. Buying the strongest reader without the right drivers leaves you stuck with a metal box that does nothing.
Hardware is just the body; software is the soul. You need comprehensive UHF RFID Reader Software Download packages with SDKs. These tools allow your IT team to customize how the reader talks to your specific database, preventing data silos and ensuring real-time updates.
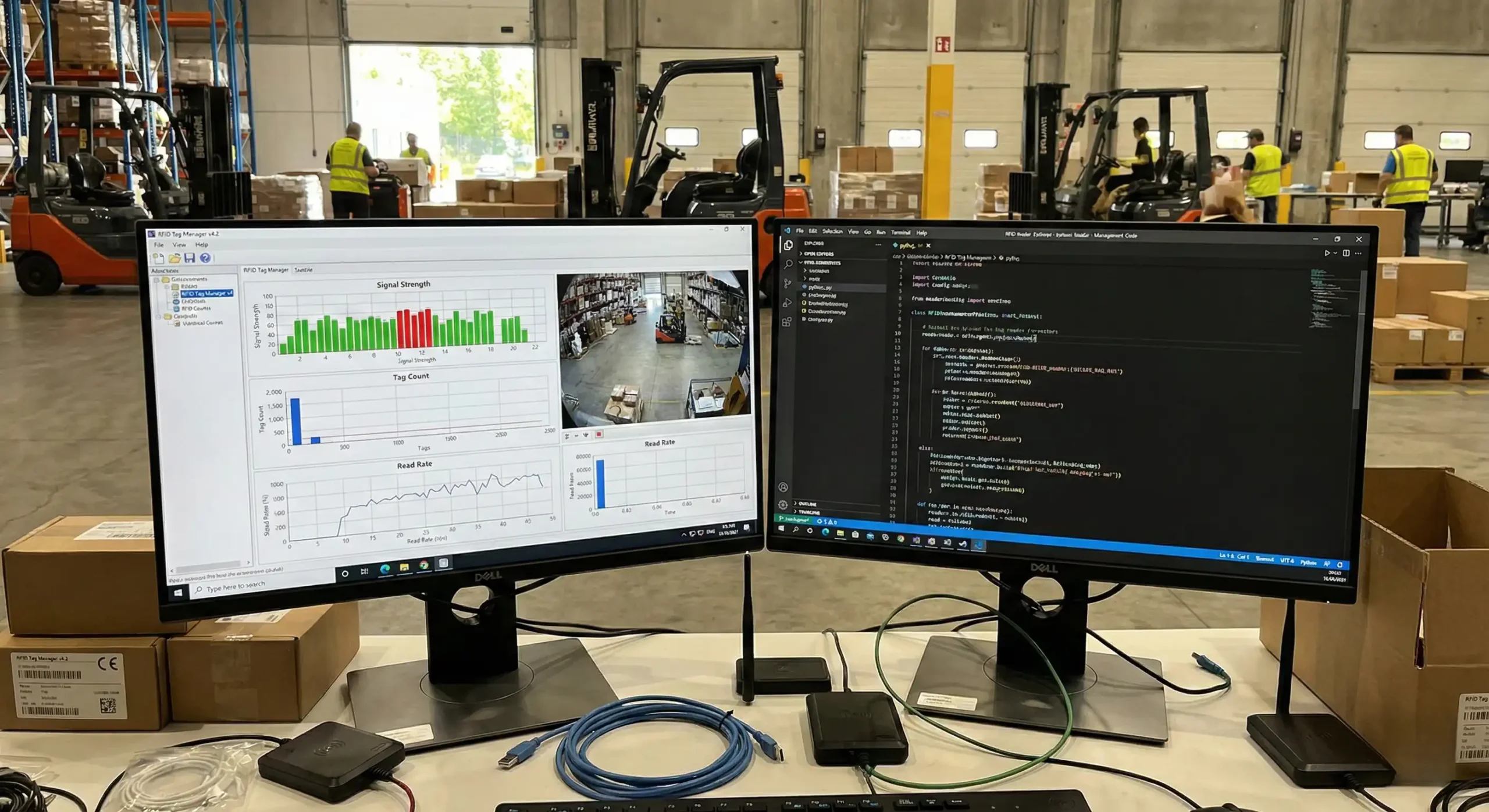
Hardware is only half the battle. I often see clients spend their entire budget on readers and forget about the integration. They end up searching for "Uhf rfid reader read and write free" online. This is a dangerous trap. These free tools are usually generic demo programs. They allow you to test if a reader works, but they do nothing for your business logic. They cannot talk to your SQL database or your ERP system.
To truly leverage RFID Write Readers in your supply chain, you need a system that supports comprehensive SDKs (Software Development Kits). At Fongwah, we provide SDKs in languages like C#, Java, and C++. This is the bridge. The reader sees a hexadecimal string like "E200 4567...". Your warehouse software does not know what that means. The SDK allows your programmers to write code that says: "When Reader A sees 'E200...', tell the database that 'Box of Apples' has arrived at 'Dock 4'."
Without this custom software layer, your reader is just beeping at you. Furthermore, software handles the "logic filtering." If a UHF Long Range Reader U6-IE-02 scans a pallet, it might see the same tag 50 times in one second. You do not want 50 entries in your database. You need the software to say, "I saw this tag, ignore it for the next 5 seconds." This logic is essential for keeping your server clean and fast.
Can Every Reader Write Data and Is It Secure?
Data breaches scare every manager. Assuming any device can rewrite your tags invites hackers and errors into your warehouse. You must know the limits of your tools.
Not all scanning devices act as an RFID Write Reader. Many hand-helds are read-only to prevent accidents. Furthermore, secure writing requires authentication passwords to access the locked memory sectors, ensuring that only authorized personnel can alter the product information.

There is a major misconception that if you can read a tag, you can write to it. This is false for two reasons: hardware capability and security permissions. First, hardware. Writing takes more power and stability. A low-battery handheld unit might fail to write, corrupting the tag. This is why we recommend desktop writers for the initial encoding process.
Second, security. In high-value supply chains, you do not want just anyone changing the data. Imagine if a thief could rewrite the tag on a $1000 smartphone to say it is a $10 toaster. To prevent this, the UHF RFID reader system uses the "Reserved" memory bank I mentioned earlier. You can set an Access Password.
When you use a proper UHF RFID Reader Software Download package, you can interface with this security layer. You can "Lock" the tag. Once a tag is locked, it becomes Read-Only. Even if someone has a writer, they cannot change the EPC code without the password. This is crucial for retail and government applications.
We also have to look at the "Kill" command. This is a privacy feature. If you sell a jacket, the customer might not want sending out a signal forever. A writer with the correct password can send a "Kill" command, permanently disabling the tag. These are advanced features that "free" generic software simply cannot handle. You need professional integration to manage the lifecycle of the tag's data securely.
Conclusion
Understanding the UHF RFID reader system means knowing that hardware captures the signal, but software creates the value. By using robust SDKs and secure RFID Write Readers, you ensure your data is accurate, integrated, and safe.
---