Executives panic over stolen credit cards, yet ignore their 15-year-old unencrypted 125kHz badge system. A $20 cloner from Amazon can compromise your entire server room in seconds. I’ve seen data centers breached because they trusted legacy proxy cards.
Enterprise-grade RFID security against skimming requires migrating from vulnerable low-frequency (125kHz) proximity cards to high-frequency (13.56MHz) encrypted smart cards. By deploying secure access control hardware with advanced cryptography (ISO 14443A) and robust SDK integration, businesses prevent badge cloning and unauthorized facility breaches at the reader level.

Let’s stop worrying about consumer tin-foil wallets and engineer a corporate access architecture that actually stops a targeted physical breach.
How Hackable Are Your Legacy 125kHz Badges and Standard RFID Chips?
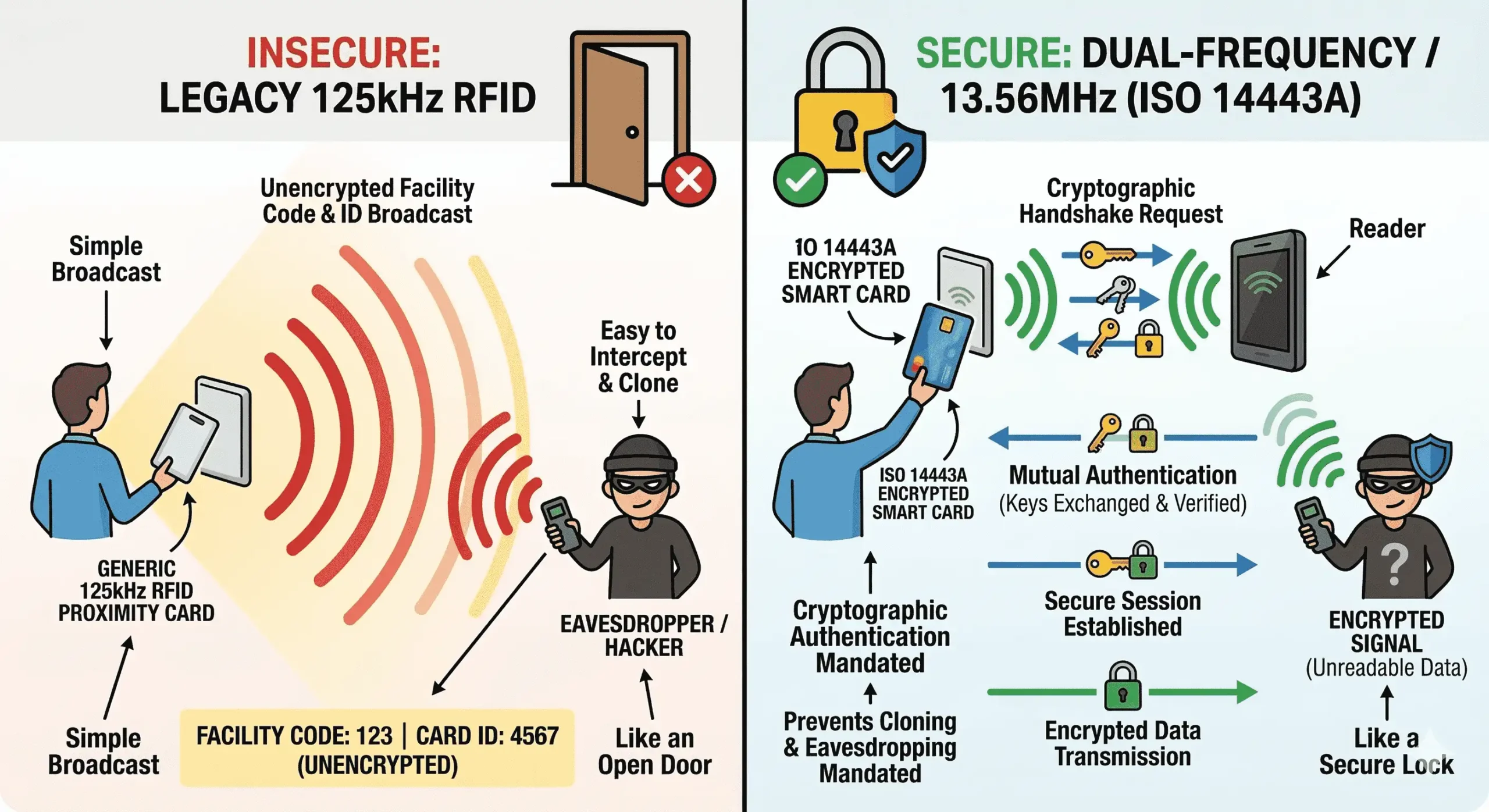
Integrators still deploy 125kHz cards because they are cheap. But these legacy chips broadcast unencrypted facility codes to anyone listening. It’s a completely open door, not a secure lock.
Standard 125kHz RFID chips are highly trackable and hackable because they lack cryptographic authentication. Upgrading to a dual-frequency or pure 13.56MHz system utilizing encrypted ISO 14443A protocols ensures that the RFID reader and smart card mandate a secure cryptographic handshake before transmitting any identity data.
William, let's look at the actual physics of a skimming attack. You wouldn't secure your corporate VPN with a plaintext password, so why are you securing the physical data center with an unencrypted proxy card?
When an attacker walks past your employee in a coffee shop with a covert skimmer, a 125kHz card simply wakes up and shouts its UID to the world. It cannot verify if the reader asking for the data is authorized.
The Phased Dual-Frequency Migration Strategy
To fix this, you don't rip and replace the whole building overnight. You use a phased hardware migration.
This is where the Fongwah E7 Desktop Reader becomes your best integration tool. It is a dual-frequency (13.56MHz & 125KHz) desktop reader with USB or TCP/IP interfaces. Because it supports our native read/write SDK, your security team can use it at the HR enrollment desk to issue new, highly secure encrypted 13.56MHz smart cards, while temporarily supporting the old 125kHz badges for legacy doors. You use the SDK to write custom cryptographic keys directly to the new 13.56MHz sectors, completely neutralizing off-the-shelf cloning tools.
Beyond providing the robust native SDK, partnering directly with an RFID hardware supplier allows for deep OEM customization. Whether your project requires specific firmware tweaks for a unique ISO 14443A deployment, or custom branding on the reader casing, having direct access to the manufacturing source eliminates the middleman and ensures your enterprise access control deployments scale profitably.
| Security Feature | Legacy 125kHz Proximity | Fongwah E7 (13.56MHz Encrypted Sector) |
|---|---|---|
| Authentication | None (Broadcasts UID) | Mutual Cryptographic Handshake |
| Cloning Difficulty | Trivial ($20 Amazon Tool) | Extremely High (Requires Key-Exchange) |
| Data Payload | Plaintext Facility Code | Encrypted Custom Applets |
| Hardware Migration | Rip and Replace | Seamless Dual-Frequency Transition |
Is Your Access Control Hardware the Weakest Link in Skimming Prevention?
You can buy the most secure encrypted RFID cards, but if your reader hardware handles decryption keys poorly or relies on vulnerable middleware, the entire corporate access system remains compromised.
Secure access control hardware must process encryption natively and interface directly with the backend. Using enterprise RFID readers that support integrated SDKs (C# or Java) allows your engineering team to control the cryptographic handshake locally, eliminating middleware vulnerabilities and preventing credential interception at the OS level.

William, I’ve audited access control systems where the "system integrator" just plugged in a generic keyboard emulation reader for a highly sensitive identity verification terminal. It’s an absolute joke. Anyone can intercept those keystrokes with a basic software logger.
If you are building an identity verification system for a government contractor, a healthcare facility, or a financial institution, you cannot rely on a reader that simply spits out a public UID into a text field. You need true Read/Write capability over the secure sectors of the credential.
SDK Control over Cryptographic Payloads
This is exactly why we engineered the Fongwah S9-BU-13-00. Designed specifically to neutralize skimming at the hardware level, it features:
Pure 13.56MHz Operation: Eliminates legacy low-frequency vulnerabilities entirely.
Dual Standard Support: Reads both Contactless (ISO 14443A/B) AND Contact smart cards (ISO 7816).
Native SDK Control (C#/Java): Bypasses vulnerable third-party Windows drivers. Your software sends the authentication command, and the reader validates the SAM (Secure Access Module).
Application-Layer Decryption: Unlike generic readers that just spit out a public UID, the S9 ensures the encrypted payload is only passed to your application after a successful cryptographic handshake.
By controlling the data flow via the SDK, you ensure the decryption happens safely within your compiled application memory.
| Architecture Component | Generic Keyboard Wedge Reader | Fongwah S9-BU-13-00 (SDK Integration) |
|---|---|---|
| Data Transmission | Emulated Keystrokes (Plaintext) | Secure API Data Payload |
| Vulnerability Profile | Susceptible to OS Keyloggers | Protected within Application Memory |
| Card Support | Reads Public UID only | Accesses Secure ISO 7816 / 14443A Sectors |
| Engineering Control | Zero | Full Control via C#/Java SDK |
NFC vs RFID Reader: Which Technology Actually Secures Corporate Identity?
Your client's IT director is asking if they can just use employee smartphones (NFC) instead of physical badges to save money. It sounds modern, but causes massive deployment headaches.
While both operate at 13.56MHz, NFC is designed for peer-to-peer consumer transactions, whereas an enterprise RFID reader is built for high-throughput authentication. For corporate identity, dedicated 13.56MHz smart cards offer superior tamper resistance, offline validation, and centralized lifecycle management compared to highly fragmented, update-dependent mobile wallets.

Let's settle the debate, William. Yes, credit cards use EMV protocols over an NFC interface (which is a subset of high-frequency RFID). But trying to shoehorn consumer NFC technology into a high-security corporate access environment is a nightmare for system integrators.
When you rely on employee smartphones for access control, you are at the mercy of Apple and Google OS updates. An iOS update can break your proprietary access control app overnight. A dead battery means the employee can't enter the building. You completely lose control of the credential's physical security lifecycle.
The Hardware Reliability Matrix
Instead, you want a dedicated, isolated credentialing system.
However, sometimes the client insists on a rapid, low-code deployment for less critical areas, like front-desk visitor management. For these specific, low-friction scenarios, you can deploy the S7-EU-00-02. It is a dual-frequency (13.56MHz & 125KHz) desktop reader strictly designed for Keyboard Emulation.
While it doesn't offer the deep cryptographic customizability of our SDK models, it strictly handles ISO 14443A/B protocols over a reliable USB interface. This allows you to instantly populate visitor logs without writing a single line of API code. The key to successful integration is matching the exact hardware architecture to the specific threat model of that specific door.
| Feature | Mobile NFC Access Control | Dedicated 13.56MHz Corporate RFID |
|---|---|---|
| Dependency | Relies on iOS/Android Updates | Independent Hardware Ecosystem |
| Availability | Fails on dead phone battery | Passive tags never lose power |
| Deployment Speed | Complex MDM software required | Instant via S7-EU-00-02 Keyboard Emulation |
| Security Lifecycle | Fragmented across personal devices | Centrally managed by IT Department |
Enterprise-Grade RFID Security & Anti-Skimming
What is the difference between 125kHz and 13.56MHz RFID security?
While 125kHz proximity cards broadcast unencrypted ID numbers that are easily cloned, 13.56MHz smart cards utilize cryptographic handshakes (like ISO 14443A) to mutually authenticate the card and the reader, preventing data interception.
How easy is it to clone a 125kHz proxy card?
Extremely easy. Because 125kHz cards lack encryption, an attacker can use a $20 off-the-shelf cloner to capture the unencrypted facility code in seconds and duplicate the badge.
Why is SDK integration important for secure RFID readers?
Using an RFID reader with a native SDK (C# or Java) allows your application to handle the cryptographic decryption locally within secure memory. This prevents vulnerabilities associated with generic keyboard wedge readers that can be intercepted by OS-level keyloggers.
Are NFC smartphones as secure as dedicated corporate RFID badges?
For enterprise environments, dedicated 13.56MHz smart cards offer better offline validation, tamper resistance, and independent hardware reliability. Mobile NFC deployments are highly dependent on fragmented OS updates and smartphone battery life, making lifecycle management difficult for IT departments.
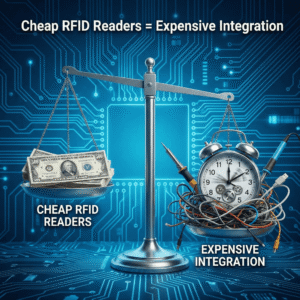
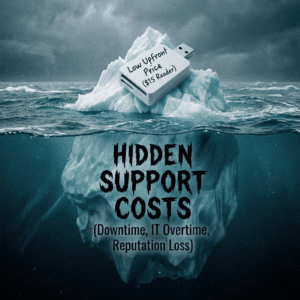
Conclusion & CTA (Call to Action): Stop bleeding engineering hours on cheap hardware. The true cost of an RFID reader is integration time. Prioritize robust SDKs and industrial stability to protect your actual project margins. Stuck on integration or sick of buggy DLLs? Ping me on WhatsApp. I'll send you a working C# sample code snippet right now.
---